The UK Government has recently published the Telecoms (Security) Bill as an amendment to the current Communications Act (2003).
This Bill comes in response to a rapid escalation in the cyber threat landscape, with relentless and sophisticated attacks targeting the country’s critical national infrastructure. The UK Government established an urgent need to compel telecommunications providers to better manage security risks within their supply chain and enhance the security and resilience of their nationwide infrastructure.
What are the implications for UK Telecommunications providers?
The new regulations will require all telecommunications providers to demonstrate to Ofcom that they have maximised the cyber protection and resilience of their networks, and optimised their security procedures. Ultimately, this will require telecommunications providers to:
- Understand and manage supply chain risk
Telecommunications providers delivering services to UK subscribers will now need to identify, document, report and respond to the threats posed by high risk vendors to ensure the security of all software and hardware deployed in their estate across the entire system development life cycle (SDLC). - Develop and sustain service resilience
Telecommunications providers will also need to ensure that critical aspects of their service are not reliant on international connectivity as part of their business continuity plan. To address this issue, telecommunications providers need to understand their current architectural deployment and which components need to re-deployed in order to support these business continuity requirements.
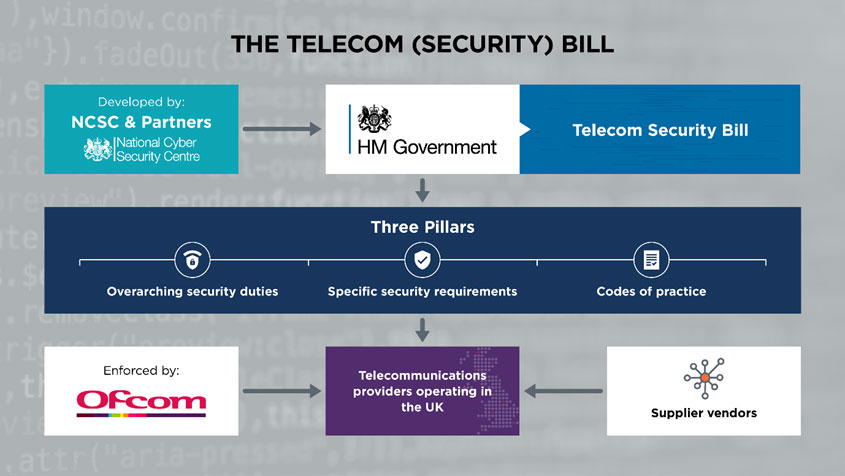
The Telecom (Security) Bill was developed by the National Cyber Security Centre (NCSC) and key partners from government, academia and industry. The Bill places a new requirement on telecommunications providers to increase the security of their operations under three core pillars:
- Overarching security duties: These will require all telecommunications providers to take appropriate and proportionate measures to identify and reduce all potential risks of systems being compromised.
- Specific security requirements: This pillar requires all telecommunications providers to strengthen specific areas such as access controls and data confidentiality, which may be exploited to compromise the infrastructure, leading to downtime and/or security issues.
- Codes of practice: This pillar addresses the appropriate timeframe for compliance for different telecommunications providers and establishes metrics and measures to be enforced.
Telecommunications providers who are audited by Ofcom may be issued with enforcement penalties of up to 10% of a provider’s turnover or £100,000 per day for non-compliance. Telecoms supplier vendors are also affected by the Bill as telecommunications providers will likely flow down responsibilities as part of the service they are procuring.
Leonardo is a trusted security partner to the telecommunications industry
As an NCSC certified consultancy, Leonardo has had sight of the Bill throughout its development and understands the detailed technical requirements needed to achieve compliance.
We have many specialist cyber consultancy teams focused purely on assisting telecommunications providers and vendors within their supply chain. Our experts can conduct a comprehensive assessment of your current operations and help you identify immediate and longer term mitigating actions to address each of the three pillars mentioned above. To illustrate this point, over the past 12 months we have helped one of the UK’s largest telco organisations understand how applicable these regulations are to them, and how compliant they are across their three largest customers.
We can also address the flow down of the regulations’ terms and liabilities between telecommunications providers and supplier vendors. Leonardo has proven expertise in this domain and can advise you how to approach this matter competently and with full confidentially.
For a free consultation regarding how to approach the telecoms security regulations, please contact david.perkins@leonardo.com.

